Principle
Minimum necessary model context
TabPro AI is designed to send only non-identifiable data to AI models as part of the workflow, not broad raw project context that is unrelated to the task.
Buyers do not need vague AI promises. They need to understand what data moves through the product, how reviewers stay in control, and how the workflow avoids turning project information into another unmanaged spreadsheet chain.
This page is intentionally focused on operating principles you can explain clearly today, without overpromising formal certifications or controls that are still evolving.
Principle
TabPro AI is designed to send only non-identifiable data to AI models as part of the workflow, not broad raw project context that is unrelated to the task.
Principle
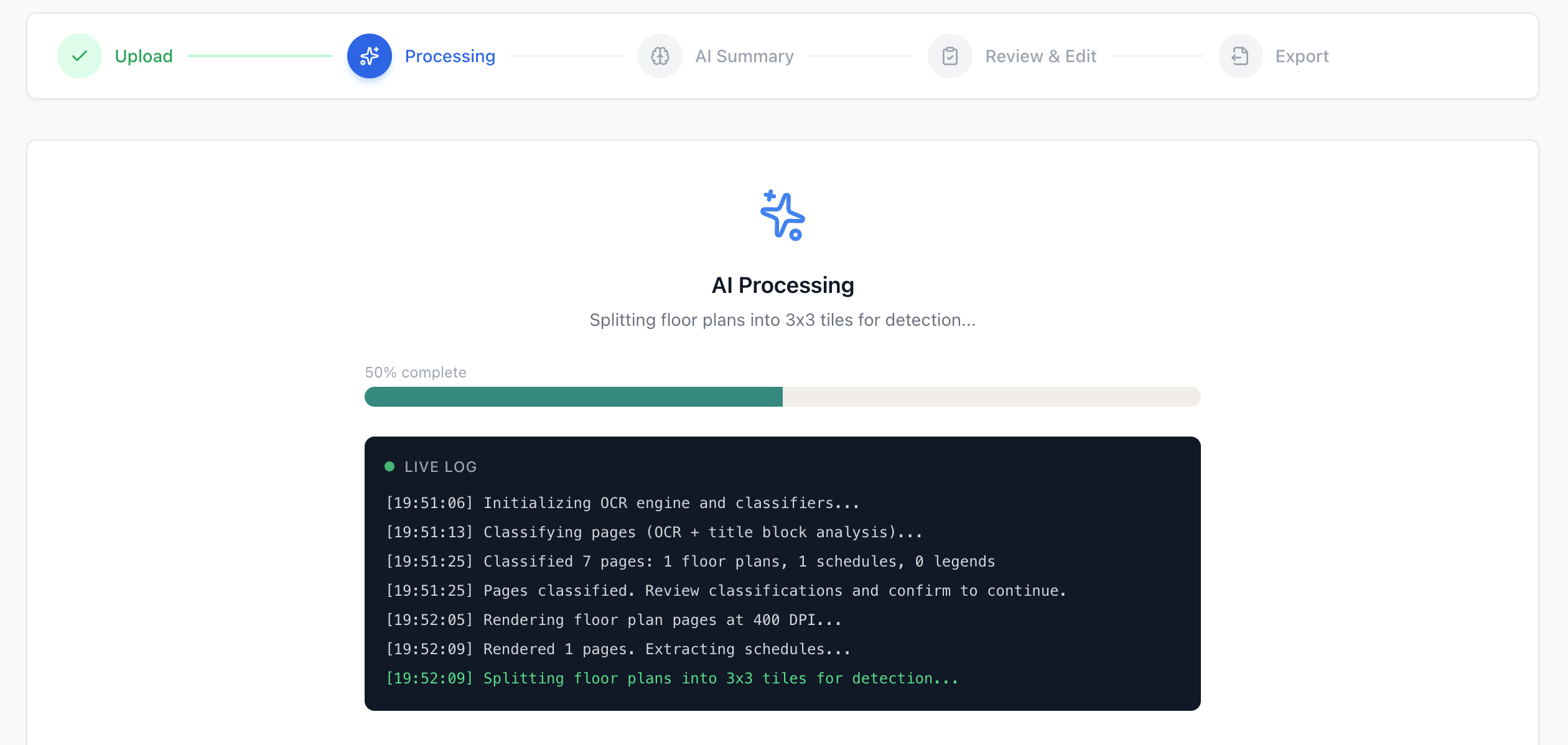
The product is built around reviewer confirmation. Extracted data can be checked against the source drawing before it moves into downstream workflows.
Principle
Reviewers can connect extracted records back to the drawing context they came from, which improves QA and reduces blind acceptance of machine output.
Principle
Keeping one reviewed dataset reduces copy-paste handoffs and spreadsheet sprawl, which also reduces data handling risk across the job lifecycle.
The strongest version of your security page is operationally honest. Explain what the product does today, what gets reviewed by humans, and which questions should be covered in a live security conversation.
Workflow visibility
Topics we should review with buyers
Security questions are best handled in context, alongside the actual workflow. That keeps the conversation grounded in how the product processes drawings, what reviewers approve, and where data moves next.